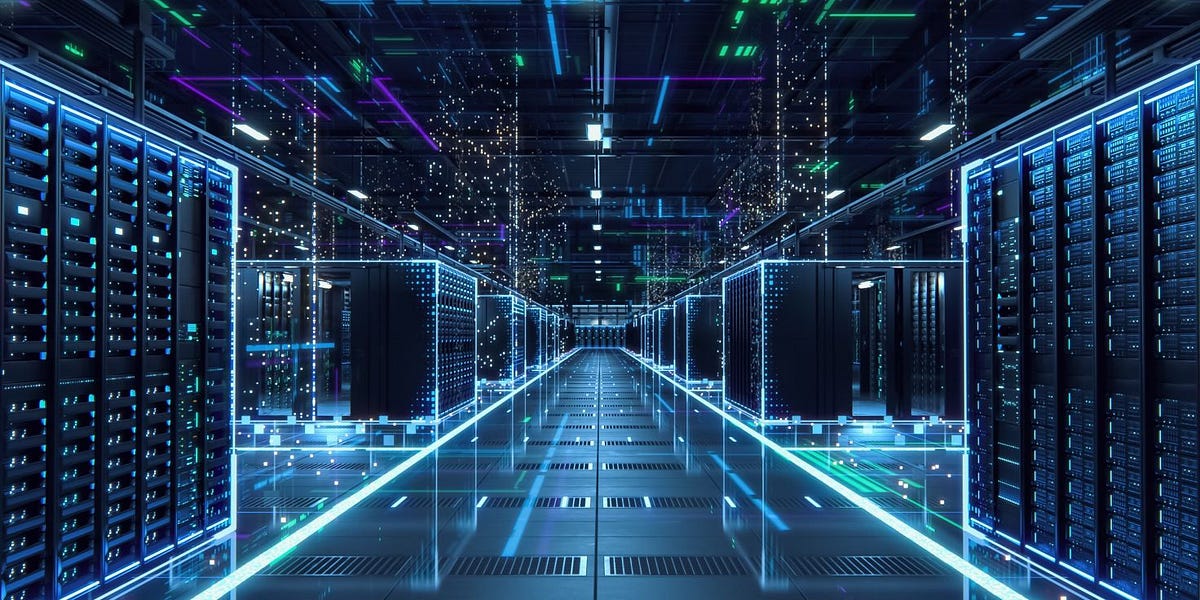
🔷 Industrial 5G & AI Cybersecurity.
Siemens combines private 5G networks with AI-driven cybersecurity.
This enables ultra-fast, secure industrial communication.
AI monitors networks continuously to detect threats.
It supports mission-critical operations in factories and infrastructure.
Advantages:
• Low latency
• High reliability
• Enhanced security
#Industrial5G, #Cybersecurity, #SecureNetworks, #AIProtection, #Connectivity
Siemens combines private 5G networks with AI-driven cybersecurity.
This enables ultra-fast, secure industrial communication.
AI monitors networks continuously to detect threats.
It supports mission-critical operations in factories and infrastructure.
Advantages:
• Low latency
• High reliability
• Enhanced security
#Industrial5G, #Cybersecurity, #SecureNetworks, #AIProtection, #Connectivity
🔷 Industrial 5G & AI Cybersecurity.
Siemens combines private 5G networks with AI-driven cybersecurity.
This enables ultra-fast, secure industrial communication.
AI monitors networks continuously to detect threats.
It supports mission-critical operations in factories and infrastructure.
Advantages:
• Low latency
• High reliability
• Enhanced security
#Industrial5G, #Cybersecurity, #SecureNetworks, #AIProtection, #Connectivity
0 Reacties
0 aandelen
2K Views
0 voorbeeld